Thank you Microsoft for changing fundamental things about your operating system, with little or no regard to those of us running in an RDS/XenApp type environment. Check out this technet article. In this article it states how changes have been made.
“In Pre-Win 8, apps could set the default handler for a file type/protocol by manipulating the registry, this means you could easily have a script or a group policy manipulating the registry. For example for Mailto protocol you just needed to change the “default” value under HKEY_CLASSES_ROOT\mailto\shell\open\command”
More importantly, you were able to use Group Policy Preferences (GPP) to set these values inside a GPO. You could also Item Level Target (ITL) them by using the GPP. This means you could easily have users run Acrobat Pro for .pdfs on SecurityGroupA and Adobe Reader for .pdfs on SecurityGroupB. However, the technet article goes on to say that in post Windows 8,
“the registry changes are verified by a hash (unique per user and app) “
A little more digging tells us that the new hashing mechanism is also on a per-machine basis. This means that a hash would be different for each user, per app, per XenApp server. Very inconvenient and annoying. This also means that we can not use the built in GPP functions in Active Directory to set these file type associations. Also very inconvenient and annoying.
James Rankin did a great blogpost on this subject as well. You can read that here. He did a great job overviewing this issue and provided a solution with using AppSense. This blog will show you how to do this with good old batch scripting and group policy. To be honest, I’m quite annoyed that I had to put together this “hack” to get around something that worked PERFECTLY FINE in 2008R2 with GPPs. If anyone has a more elegant solution, I’d love to see it. I’m not the best scripter in the world, but I’m very pragmatic. “It works”
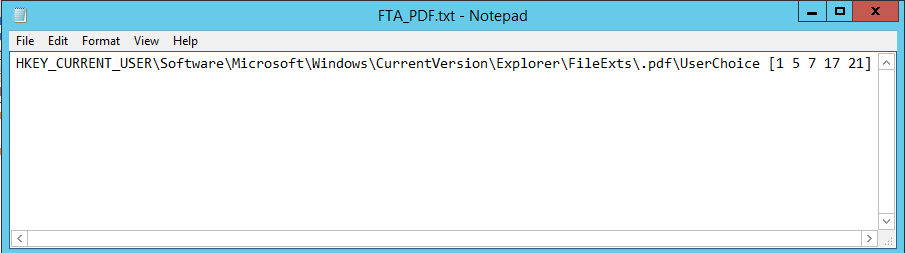
The first thing we want to do is create a logoff script to delete HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.pdf. However, because of that pesky Deny in the UserChoice key, we are unable to simply do this. So, I have made a simple “regini” command to overwrite the permissions on that key so that we can delete. In my environment, I have created FTA_PDF.txt in the NETLOGON directory. Inside this file is simply a registry value and some codes, which allow SYSTEM, Administrators, Interactive User, etc, FULL CONTROL of the key.
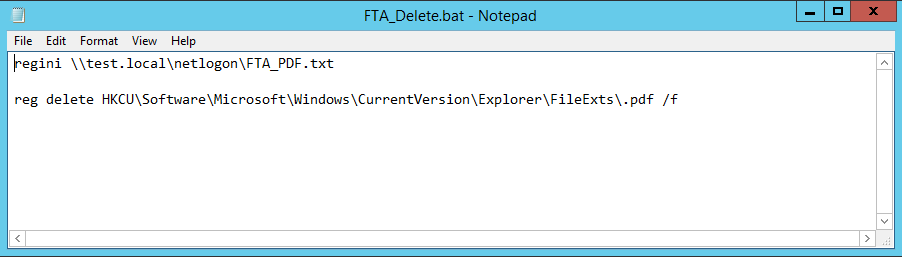
Next, I create a FTA_Delete.bat file in NETLOGON. This runs the “regini” command to change the permissions, then a “reg delete” command to delete the key.
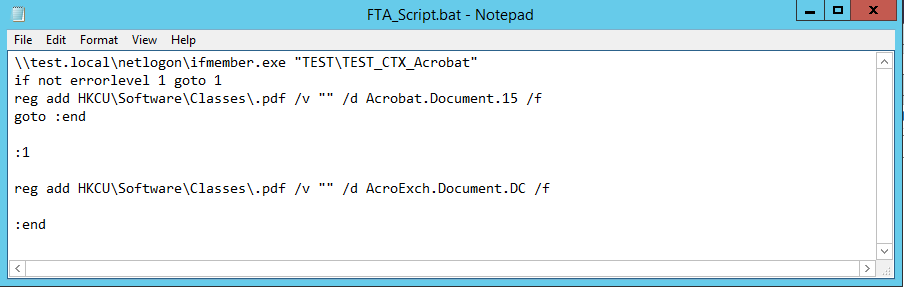
Then we need to create the script for the logon process. I’ve busted out good old “ifmember” for this one. It’s a simple executable that will check AD group membership. My script is pretty simple. It checks to see if a user is a member of the Acrobat group. If so, run the “reg add” to add the association to Acrobat. If not, it falls back to the default .pdf reader in this environment. In this case, it’s Adobe Reader. Keep in mind that you can add multiple programs and associations using this method. You can add Foxit here if you would like.
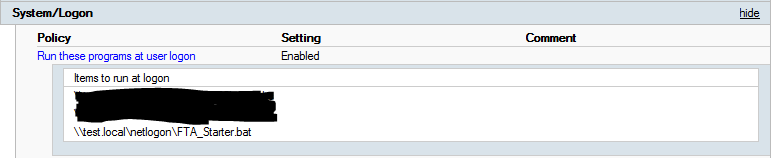
So, the sad fact of the matter is when I tried to set this as an actual “Logon Script” the functionality didn’t work. I had to set this in a User GPO: Administrative Templates\System\Logon\Run these programs at user logon. I’m also the type of person that hates to see a CMD window flash up on the screen right after I login. So, I wrote ANOTHER script called FTA_Starter.bat to call this script to run in a minimized window.
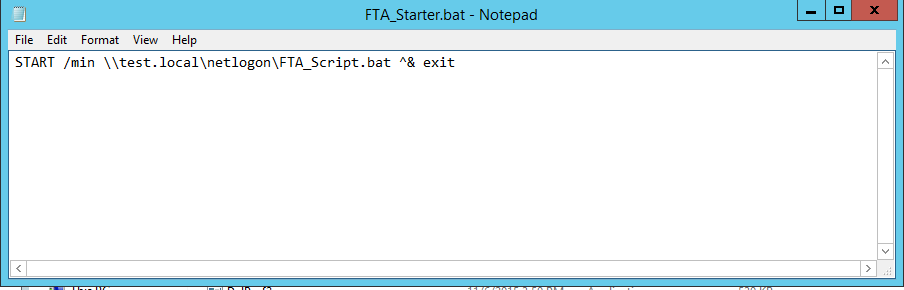
This is the script I added to the GPO.
So, I fought with this for a long time and it wasn’t working. I had to re-read James’s blog and found this little blub at the bottom.
“Update – I built a third XenApp server, just to be sure, and this time the solution wouldn’t work until I removed the Registry key HKLM\Software\Classes\.pdf.”
This DID NOT WORK until the HKLM key was deleted from the servers. Do not forget this step.
I hope this helps you work through this issue in less time that it took me to do it.

Hi. We are not able to get this to work. Sometimes it will set the filetypes and sometimes it won’t. We have tryed to set a pause in the script running at logon so it don’t run directely but instead waits for 15 sec (or more) but that did not help. Anyone that have had same problem? Or anyone that knows what could be wrong?
We don’t use Citrix Profile Management.
We need this because we have diffrent license groups. Some users have Office 2013, some users have Office Viewers and some have LibreOffice.
The only issue I saw that was similar was if I tried to click a PDF file (or whatever file type i was changing) before the script had time to run. I’d be happy to help you with this. Jump in the IRC channel and we can figure it out.
Have the same problem, want to use LibreOffice and Office 2013 par group of user in remoteApp, if you have find a solution could you tell me the way you got it,
Hi Ryan.
I was in the IRC webIRC but can’t find You there and when asking for You I gon no result. 🙂
I see You are from Columbia and I’m from Sweden and we are in a timezone that are 7 hours later than you..So here it’s 16:10 and at You it’s just 9:10.
What time is the best time for you and what is your nic in IRC??
I see you in there now. 🙂
Hey Ryan,
Great post! This certainly helped me find the solution for my environment.
I did however, tackle this issue differently.
I used a GPP to delete the key under HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.pdf and then do an update on the key under HKCU\Software\Classes\.pdf while also deleting the key under HKLM as mentioned.
In my testing this works perfectly and should also provide an easier solution.
You could also use this in conjunction with Item-Level Targetting when going through the update of the HKCU\Software\Classes\.pdf which would allow different applications for different security groups.
Glad to see this method worked. I generally tackle things with GPP as well. I will have to test this out too. Thank you for the comment!
The GPP method worked well for me too (with Item Level Targeting and NOT selecting “Run in logged in user context”).
I still had to remove the .pdf key from HKLM before it will work.
This worked well in my Server 2012 R2, XenDesktop 7.6 farm.
Thanks for the input!
Hey everyone
I put an update out to the original article I did around this – http://appsensebigot.blogspot.co.uk/2016/05/deploying-per-user-file-type.html
I seem to have come down on the exact way Marvin mentions above to set the FTAs through GPP – I’ve also put a bit of PowerShell and AppSense together to try and “roam” the FTA settings from device to device. Works well with PDF, VSD, JPG and the like – Office documents and browsers I have found considerably more challenging.
Cheers,
JR
i have built a utility for windws 10 and server 2016 which can set file type associations per user: SetUserFTA
it will calculate the hash for the userchoice key and set it automaticly to the registry.
SetUserFTA: http://kolbi.cz/blog/?p=346
Thanks, Ryan, James and Kolbicz!!! Great stuffs!
Hi Kolbicz,
Does SetUserFTA work with Windows Server 2012 R2?
Regards
yes. i have updated it to support win8+ and server 2012+
For Print (context menu) and Quick Print (Outlook), consider the editing the following:
Open registry to:
HKEY_CLASSES_ROOT\AcroExch.Document.DC\shell\Print\command
Change value to Reader:
“C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe” /p /h “%1”
[…] The trickiest bit is elevation of privilege for the HKLM removals, which is where AppSense EM makes everything so much easier (SYSTEM elevation as a tick-box). I believe Ryan Gallier did some work around this in batch on CitrixIRC […]
I don’t even know the way I finished up
here, but I assumed this publish was great.
I don’t recognize who you might be however definitely you’re going to a famous blogger for those who aren’t already.
Cheers!